I exposed a pedophile network; France is acting, the US is not.
The pedophile network I exposed was investigated within 24 hours, the US has been silent
After writing my first piece, I was contacted by a few journalists. One of which was Arnaud Wajdzik, a respected journalist of 30 years with Ouest France. Arnaud was requesting more information on any french clusters in the network. After a short back and forth, he asked if I had ever heard of an abusive ecosystem named "cocoland". I hadn't but dug in and found some alarming things. On May 2, 2026, he published, the same day the high courts opened an investigation.
Cocoland started as coco.fr: founded 2003 by Isaac Steidl, Italian national, with €2,000 from his parents. Designed as anonymous no-registration chat, it became France's most
documented predator platform.

- Cited in 23,051 judicial proceedings in under four years. Used by Dominique
Pelicot from 2011-2020 to recruit the hundreds of men who raped his wife Gisele after he drugged her. - December 31, 2020 the day after Pelicot's arrest Steidl re-registers under
coco.gg (.gg = Guernsey, outside French jurisdiction). Deliberate legal evasion. - June 2024: French prosecutors via Eurojust shut it down. July 2024: two
moderators arrested. January 2025: Steidl arrested, €5M seized, charged with
child pornography, corruption of minors, pimping, drug trafficking and money laundering.
But Arnaud was asking if I had heard of the website popping back up anywhere. A quick Yandex search showed dozens of copycat sites, but one stood out among the rest, cocoland.cc. I'd like to preface this with the fact that Steidl and his lawyer both deny any involvment with this new site, and although I can't refute that, I can say for certain this person had a full copy of the entire coco.gg infustucture and were ready to put it back up. Cocoland.cc self-identifies as coco.gg continuation (an old /sites/ page lists coco.gg as "former domain (blocked)" but they've taken it down since the piece by Ouest France) it even has the subdomain "coco.gg.cocoland.cc", which is pretty damning. The ToS page (/chat/regle.html, also taken down) was also completely copy pasted from the original coco.gg site, they didn't even bother to update it. At the time of this post, cocoland.cc is serving a fake "gaming" home page to get passed google audits, which is a good idea since I found they have 52 google analytic ID's connected to the same account. That is very against googles TOS, but it's obviously been working for them for a while. All of that is alarming, but what if I told you coco.gg is still active?
Evidence of continued active operation:
- SSL certificates auto-renewing continuously every ~90 days: March 2025, May 2025, July 2025, September 2025, November 2025, January 2026, March 2026, someone is running certificate automation
- Two parallel cert issuers simultaneously: Let's Encrypt (E5/E6/E7) AND Google Trust Services (WE1) active dual-CA setup
- Current hosting: dataforest GmbH, Frankfurt DE (AS58212) — dedicated IP 45.145.41.54, PTR: 54.41.145.45.dataforest.net — private German host, NOT a law enforcement sinkhole
- Active mail server: mail.coco.gg → 87.106.65.135 (IONOS, London)
- Active SPF:
ip4:51.158.201.0/24— Scaleway Paris range (French company) - New GSC token:
IAt6ZI9bEnQIKJt97hXQZcCGgoU2UM4UrF1ixwttYhs— different Google account from cocoland.cc token (X3vi2cUqw...) — two separate verified Google identities across the two domains - Domain status: Active, locked (Delete/Update/Transfer Prohibited by Registrar) — likely registrar hold post-seizure, but infrastructure is live
- Registrar: Enrapture Limited (https://enrapture.gg) — Channel Islands (.gg TLD), registered through Channel Island Hosting. Enrapture holds Steidl's registrant data. Registry: CIDR (Channel Islands Domain Registry / Island Networks, Guernsey)
- Stripe payment integration: payment.coco.gg CNAME → hosted-checkout.stripecdn.com — Stripe hosted checkout was active on coco.gg. Stripe requires full merchant KYC: government ID, bank account, tax ID, business registration. Stripe holds the users verified financial identity. (Currently returning CF 403 "DNS points to prohibited IP".)
That's right, Stripe has an active account with payment.coco.gg, and is even being directed to the website when entering that subdomain. How they have been able to get around those guardrails is beyond me, but as of writing this post it's still seems active.
Nmap result show: 3389/tcp OPEN ms-wbt-server being the only port open.
- The server is Windows — RDP (Remote Desktop Protocol) is Microsoft-only. This is a Windows Server machine on dataforest GmbH Frankfurt.
- No web server running — no HTTP (80), no HTTPS (443), no other services. The origin is intentionally dark. Cloudflare handles external DNS/routing; this box serves no direct web traffic.
| Domain | Status | Purpose | Host/CDN |
|---|---|---|---|
| cocoland.cc | LIVE | Main platform — coco.gg relaunch, self-identified. Homepage is fake "Mini Games" AdSense cover page. | Cloudflare CDN → BlazingFast NL |
| cocotchat.net | LIVE | Sister domain — same CF account (jaziel+becky). cPanel live at origin 185.62.188.4:2083. Discord integration. Cert SAN alias: cocotchat.net.cocoland.cc. | Cloudflare → BlazingFast 185.62.188.4 |
| pix1/2/3.cocoland.cc | LIVE | Image servers | Cloudflare |
| vid5.cocoland.cc | LIVE | Video server | Cloudflare |
| vid.cocoland.cc | LIVE | Additional video server | Cloudflare (104.21.42.95) |
| video.cocoland.cc | LIVE | Additional video server | Cloudflare (104.21.42.95) |
| sms.cocoland.cc | LIVE | SMS verification | Cloudflare |
| pay.cocoland.cc | Enumerated | Payment processing | Cloudflare |
| stream.cocoland.cc | Enumerated | Streaming | Cloudflare |
| cloud1.cocoland.cc | Enumerated | Cloud storage | Cloudflare |
| dev.cocoland.cc | Enumerated | Active development | Cloudflare |
| discord.cocoland.cc | Enumerated | Discord integration | Cloudflare |
| blog.cocoland.cc | Redirects → www | — | Cloudflare |
| mail.cocoland.cc | Redirects → www | — | Cloudflare |
| ftp.cocoland.cc | Enumerated | FTP — no A record | — |
| gg.cocoland.cc | Enumerated | — no A record | — |
| coco.gg.cocoland.cc | LIVE redirect | Legacy coco.gg branding preserved | Cloudflare |
| pix1/2/3.coco.gg.cocoland.cc | LIVE | Old coco.gg image servers mirrored under new domain | Cloudflare |
| coco.gg | ACTIVE post-seizure | SSL certs auto-renewing Mar 2025–Mar 2026; dataforest GmbH DE; active mail. See above. | dataforest GmbH Frankfurt (AS58212) 45.145.41.54 |
| payment.coco.gg | CNAME → Stripe | Stripe hosted checkout — Stripe holds merchant KYC | Cloudflare → Stripe |
This means someone is remotely signing in to a windows server from somewhere else, possibly managing things from a secondary location.
So it's not a hidden ecosystem, but it's hard to argue this isn't someone very involved in the operations of the old coco.gg.
Between October 2015 and early 2016 all of the following resolved to 91.121.221.218 simultaneously. A KimSufi dedicated server is not shared hosting — every domain on it belongs to the same operator. All share an identical lifecycle: registered 2015, moved to KimSufi late 2015, Cloudflare added 2016, went dark 2017, reactivated 2026.
cocoland.info mail.cocoland.info
cocoland.org mail.cocoland.org
loovchat.com mail.loovchat.com
le-chat-gratuit.com mail.le-chat-gratuit.com
tchat-en-direct.com
rencontresansinscription.com mail.rencontresansinscription.com
avisrencontre.com
reponses.org
rencontre.ma
dilandau.biz mail.dilandau.biz
Domains (Current Portfolio)
| Domain | Status | Purpose | AdSense | Notes |
|---|---|---|---|---|
| loovchat.com | LIVE | Main chat platform | pub-5757889076387891 | — |
| rencontres.loovchat.com | LIVE | EasyFlirt white-label | — | AS21217 backend |
| mail.loovchat.com | LIVE | Drupal chat directory | — | /admin/ exposed, unmaintained |
| cocoland.org | LIVE | Coco clone, markets to teens | pub-5757889076387891 | Reactivated March 30, 2026 |
| cocoland.info | LIVE | EasyFlirt white-label + IRC chat | pub-6787975972465738 | — |
| chat-coco.com | LIVE | French chat — Actor 2 confirmed | unknown | kiki+sam NS + EasyFlirt source=chat_coco_com affiliate confirmed |
| fr-chat.com | LIVE | French chat — "adolescents" listed as target | pub-5757889076387891 | Anonymous, no registration |
| fr-tchatche.com | LIVE | French chat | pub-6787975972465738 | — |
| sitetchat.com | LIVE | French chat | pub-6787975972465738 | Dedicated /chat-ado page |
| chatgratuit.club | LIVE | Free chat | pub-5757889076387891 | — |
| voirsite.com | LIVE | Web directory | pub-5757889076387891 | — |
| rencontresansabonnement.com | LIVE | Dating no subscription | pub-5757889076387891 | — |
| rencontresansinscription.com | LIVE | Anonymous chat — dedicated under-17 room | unknown | Reactivated Feb 17, 2026. kiki+sam NS confirmed. No MX. Most urgent finding. |
| avisrencontre.com | LIVE | SEO "review" site for own platforms | unknown | Reviews /cocoland, /easyflirt, /bounty-chat-avis-complet |
| tchat-en-direct.com | LIVE | French chat | unknown | — |
| rencontre.ma | LIVE | Moroccan market | unknown | — |
| buzzici.com | LIVE | Unknown | pub-6787975972465738 | — |
| favorisweb.com | LIVE | Web favourites | pub-6787975972465738 | — |
| sexmy.net | LIVE | Adult video platform | none visible | DNS history pending |
| le-chat-gratuit.com | NXDOMAIN | French chat | unknown | Lapsed |
| reponses.org | NXDOMAIN | French Q&A / SEO | unknown | Lapsed |
| dilandau.biz | Reactivated on JP hosting | Piracy mirror | — | Now muumuu-domain.com — likely different operator acquired expired domain |
The bridge account (pub-2865330840951074) ties both cluster identities to a single payment record at Google. Separate accounts for cocoland.org (teen-targeted) and cocoland.info likely indicate risk compartmentalization, so if cocoland.org gets banned, cocoland.info stays live. The most alarming piece is the dedicated under-17 chat room rencontresansinscription.com. An anonymous, no-registration chat for children under 17. Footer cross-links to cocoland.info and loovchat.com. Affiliate paths /p_302 and /p_320 redirect to literal adult dating services. fr-chat.com also explicitly lists "adolescents" as a target user demographic. All very alarming, took less than a day for the courts to act once I found all of this and sent it to Wajdzik for the piece he was working on. Wajdzik then asked about the french versions of the boychat/free spirits ecosystem. Not speaking french, but eager to help, Claude and I dove into the infamous Legarcon.net.
Created in 1999, Legarcon is one of the longest running "boylove" message boards. With 400,000+ archived posts it is still live and active today. But after Ouest France released their piece on this online network, a now deleted post on Legarcon by user "Tristan" posted
""Helgé [legarcon.net] is under investigation by the French government. I'm just noting that foreign contacts have very, very compromising information on the following matters: — The Epstein file in France, a guy who had an apartment near the Arc de Triomphe with cameras that recorded videos of personalities close to the responsible Sarah El Haïry — The Palmade affair, where certain members close to the government are implicated... These files are held outside France, by people who are indebted to us. So, Miss Sarah El Haïry, watch your ass! PS: I use proxies in multiple countries..."
Immediately following this post, Sarah El Hairy, who is the Haute-commissaire à l'Enfance (High Commissioner for Children/Childhood), is quoted saying These threats “will only strengthen my determination to shed light on these facts and to hunt down, denounce and fight unabated child crime,”. Almost immediately an investigation was underway, showing the priority they have for protecting children. In contrast, nothing public has been stated by the US about any sort of investigation.
New findings and a reply to "Brian Ribbon"
"Hell, they could magically persuade every country in the world to criminalize our very existence as MAPs, and then we'd have absolutely nothing left to lose! If they wanna start a war, bring it the fuck on!"
Brian made many inflammatory statements against the French government and my friend Arnaud Wajdzik following the statements by the French High Courts. Even threatening violence against a country he is supposedly thousands of miles away from. I thought refuting his points would be the best way to get into the biggest finding so far! Warning: I get technical here, I'll do a TLDR afterwards.
As I mentioned in a prior article, someone calling himself a cybersecurity researcher recently discovered that many of the clearnet MAP sites share a common hosting platform. His technical analysis was correct, relying on public information that can be interpreted by almost anyone vaguely familiar with networking. His inference regarding what that meant about how clearnet MAP sites are organized? Not quite on the mark. His assumption that I'm essentially the king of pedos was quite hilarious. - Brian Ribbon
One Naming Backbone to Rule Them All:
Brian is half right. I did rely on public information. The inference about organizational structure, however, is exactly on the mark, and the evidence that proves it isn't the shared hosting or the shared mail server. It's a private internal DNS zone that was obviously supposed to be hidden.
What Brian Is Right About
My original finding, that many MAP clearnet sites share a common hosting platform and mail server, is technically accurate. Brian's response to it is also technically accurate: sharing a hosting provider and mail server does not, by itself, prove top-down coordination. Lots of unrelated organizations use FranTech/BuyVM because it has a permissive acceptable-use policy. Lots of organizations use the same mail infrastructure because someone set up a shared relay and offered it to affiliates.
Brian is correct that this alone doesn't prove he's "king of pedos." It doesn't prove a command structure. It doesn't prove a single operator.
What does?
isp-cx-miami.net
isp-cx-miami.net is a domain registered November 18, 2010, maintained under NameSilo's PrivacyGuardian protection, with DNS managed through Hetzner's default nameservers. It has no public website. It is not listed anywhere. It is not linked from any of the sites in this network.
It is a private internal DNS zone — a naming system that assigns human-readable hostnames to servers across multiple hosting providers and countries. Its only purpose is to let one operator (or a small admin group) refer to their servers by name instead of IP address.
The reason it's findable at all is a side effect of how PTR records work. When a hosting customer sets a custom reverse DNS entry on their server's IP address, that entry is publicly queryable by anyone who knows the IP. Operators who do this reveal the naming scheme they use internally.
The operator of this network set custom PTR records on many of their servers. Those PTR records point back to isp-cx-miami.net. The naming scheme they used tells you everything.
What the Naming Scheme Proves
As of April 2026, the isp-cx-miami.net zone contains 51 named hosts. The names are not random. They follow a deliberate, internally consistent taxonomy that directly maps to the network's organizational structure.
"fs-" prefix — Free Spirits infrastructure
| Hostname | IP | Role |
|---|---|---|
fs-ns1.isp-cx-miami.net |
192.227.152.179 | Shadow authoritative nameserver for boychat.org |
fs-ns2.isp-cx-miami.net |
45.130.22.168 | Shadow authoritative nameserver for boychat.org |
fs-ns3.isp-cx-miami.net |
85.121.240.214 | Shadow authoritative nameserver for boychat.org |
fstvidarch.isp-cx-miami.net |
205.185.126.8 | fstube.net video archive backend |
fs-eunl.isp-cx-miami.net |
(dormant — planned NL node) | Free Spirits Netherlands expansion |
fs-usla.isp-cx-miami.net |
(dormant — planned LA node) | Free Spirits Los Angeles expansion |
fs-usny.isp-cx-miami.net |
(dormant — planned NY node) | Free Spirits New York expansion |
The operator uses the fs- prefix to label their own Free Spirits-aligned boxes in their private inventory. They label the shadow nameservers for boychat.org with this prefix. They label the fstube.net video archive backend with this prefix. These are not labels assigned by outsiders. These are internal names the operator chose for themselves.
"al-" prefix — aldns.org / Mu / MAP Union infrastructure
| Hostname | IP | Role |
|---|---|---|
al-ns1.isp-cx-miami.net |
45.10.20.115 | Identical to ns1.aldns.org |
al-ns2.isp-cx-miami.net |
81.181.106.109 | Identical to ns2.aldns.org |
al-ns3.isp-cx-miami.net |
154.19.184.101 | Identical to ns3.aldns.org |
al-uklo.isp-cx-miami.net |
(dormant — UK London node) | Planned alentogroup expansion |
al-usla.isp-cx-miami.net |
(dormant — US LA node) | Planned alentogroup expansion |
al-usmi.isp-cx-miami.net |
(dormant — US Miami node) | Planned alentogroup expansion |
The al- prefix is the private internal name for what the public sees as ns1/ns2/ns3.aldns.org — the authoritative DNS infrastructure for MAP Union, brianribbon.com, nambla.org, yesmap.net, fstube.net, newgon.net, annabelleigh.net, and a dozen other sites. Same physical servers, two names: one for the public, one for the private inventory.
The shared mail server
| Hostname | IP | Role |
|---|---|---|
roman.isp-cx-miami.net |
185.250.106.93 | box.isp-email.net — the Mail-in-a-Box installation serving as shared mail for the entire North American cluster |
This server provides email for the following confirmed domains: boychat.org, boy.chat, boylinks.net, boylinks.org, boywrite.ivan.net, lifeline.chat, ivan.net, freespirits.org, freespirits.info, jungsforum.net, castilloazul.org, legarcon.net, map-union.org, yesmap.net, boymoment.com, boymoment.net, annabelleigh.net, cblf.org, mhamic.org, nambla.org, glgarden.org, and brianribbon.com.
The Free Spirits forums (boychat.org), the MAP Union flagship (map-union.org), NAMBLA (nambla.org), and Brian Ribbon's personal blog all receive mail through a single Mail-in-a-Box installation named roman in the operator's private inventory. A Mail-in-a-Box installation requires deliberate per-domain configuration by an administrator. This is not a coincidence of shared hosting. This is a single administrator configuring mail for all of them.
Site servers named in the same scheme
| Hostname | IP | Role |
|---|---|---|
wynwood.isp-cx-miami.net |
104.244.78.135 | brianribbon.com |
brian.isp-cx-miami.net |
104.244.79.60 | Second dedicated Brian Ribbon server |
robin.isp-cx-miami.net |
104.244.76.167 | Named after John Robin Sharpe |
Three things worth noting here.
First: Brian Ribbon's website server is named wynwood — a Miami neighborhood — in the operator's private naming scheme. The same person who named the boychat.org shadow nameservers fs-ns1 named Brian's server wynwood.
Second: Brian Ribbon has two entries in this private inventory. wynwood.isp-cx-miami.net is his live site. brian.isp-cx-miami.net (104.244.79.60, FranTech) is a separate, distinct server assumed to be named directly after him. They maintain a second FranTech server in his name. Independent sites operated by unaffiliated people don't get two named slots in someone else's private VPS inventory.
Third: robin.isp-cx-miami.net is named after John Robin Sharpe — convicted in 2002 for possession of over 400 child pornography images and convicted in 2004 for sexual contact with a child. His websites, robinsharpe.ca and robinsharpe.org, remain live today on ns1.aldns.org. The operator named a server after him. The naming backbone that hosts Brian Ribbon's server infrastructure also celebrates a convicted child abuser by name.
The Single-Operator Proof
A private internal server naming convention that simultaneously assigns names to:
- Free Spirits' hidden backup nameservers (
fs-prefix) - The free speech video platform's archive backend (
fstvidarch) - The MAP Union / aldns.org public nameservers (
al-prefix) - The shared mail server serving both clusters (
roman) - Brian Ribbon's live website (
wynwood) - A second dedicated Brian Ribbon server (
brian) - A server named after a convicted CP offender (
robin) - Planned geographic expansion nodes for both clusters (
fs-usla,al-uklo,eunl,eubg, etc.)
...cannot exist without a single coordinating administrator.
PTR records are set by the entity that controls the IP address. Custom PTR records require deliberate action by the hosting customer. The hosting provider does not name your server. You name it. The operator who named roman.isp-cx-miami.net and fs-ns1.isp-cx-miami.net and wynwood.isp-cx-miami.net is the same person managing a unified infrastructure that serves what Brian Ribbon characterizes as separate, unrelated communities.
The fact that querying roman for zones outside the Free Spirits cluster returns REFUSED — that the infrastructure maintains operational partitioning between clusters — does not disprove unified administration. It proves it. Someone who understands both systems well enough to partition them deliberately is someone who administers both.
The Depth of the Record — Not a Recent Coincidence
This infrastructure did not coalesce recently. The aldns.org authoritative DNS record shows continuous unified administration going back to at least August 2011, the earliest confirmed domain on the same nameservers. A partial timeline:
| Domain | On ns1.aldns.org since | Notes |
|---|---|---|
glgarden.org |
August 2011 | 7 continuous years, then migrated |
somersaultforums.org |
July 2012 | Named after Ian Hodgson, convicted in 1990 for sexually assaulting students aged 11–15. Still an active Free Spirits member at time of domain creation. |
annabelleigh.net |
August 2013 | GirlChat — continuous to present |
alentogroup.org |
July 2013 | Earliest documented co-administration of operator infrastructure |
nambla.org |
March 2018 | NAMBLA moved its DNS to this operator |
fstube.net |
June 2023 | PeerTube video platform |
brianribbon.com |
May 2025 | Brian's blog |
This is 15 years of the same operator managing the same set of communities under the same DNS backbone. The claim that these are "independent communities that just happen to share infrastructure" requires believing that unaffiliated operators independently arrived at the same private naming convention, the same mail server, and the same DNS infrastructure, and maintained that coincidence for a decade and a half.
The Door to the Kingdom
Among the 51 named hosts in the isp-cx-miami.net zone is one that has no public-facing function at all:
idlers.isp-cx-miami.net — 178.63.82.37 — Hetzner Online GmbH, Germany (AS24940)
This server runs MyIdlers, a self-hosted VPS inventory management application. It is the operator's private dashboard for tracking every server they own: provider names, account credentials, billing information, server specs, and IP allocations across all hosting providers.
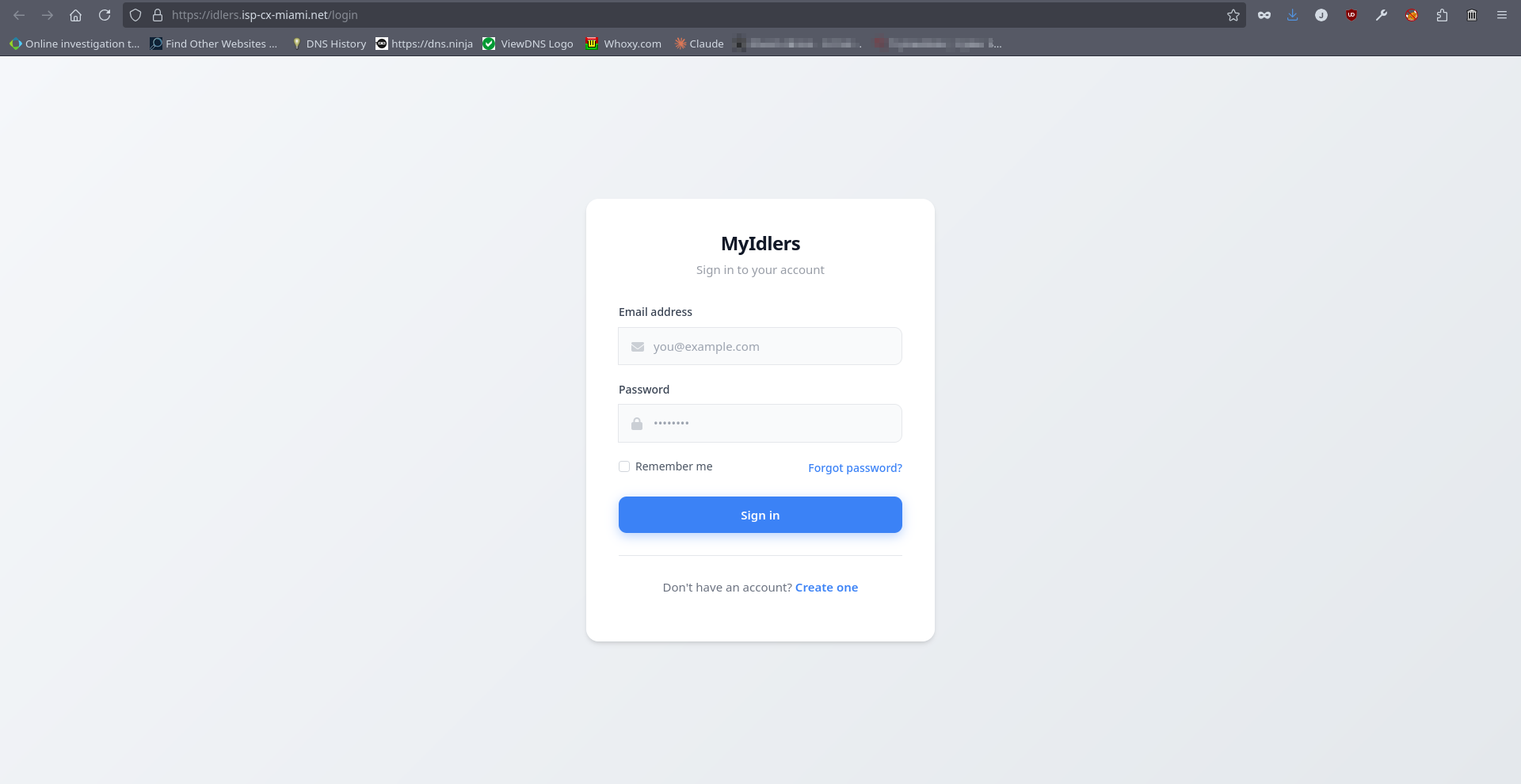
The public-facing login interface is live at that IP. It has a /login page, a /register page, and a /forgot-password page. The operator's complete infrastructure inventory — every provider, every account, every server exists behind that login.
The significance of this from a technical standpoint is that the operator keeps all of their server records in one place. That place has a name in their private naming backbone. That name resolves to a Hetzner Germany IP address.
The same Hetzner account also holds the DNS zones for isp-cx-miami.net and w3fora.net (a related internal operations stack). A single legal process request to Hetzner surfaces the identity behind all of them.
The operator named their VPS inventory tracker in the same private backbone they use to run a network of pedophile advocacy sites. It is, in the most literal sense, a door: the login page that separates the public from the complete map of who is paying for all of this.
TLDR: Every server in this network has a private nickname — like calling your computers "roman" or "wynwood" instead of their IP addresses. These nicknames are only visible if you know where to look, and the network's operators clearly didn't think anyone would. Those nicknames tell the whole story. Free Spirits servers are labeled "fs-". MAP Union servers are labeled "al-". Brian Ribbon's website sits right next to them, labeled "wynwood." NAMBLA's mail runs through the same server as Brian's blog. A server is named after a convicted child pornographer. All of it, every
cluster Brian claims is independent, lives inside the same private naming system, managed by the same person.
His assumption that I'm essentially the king of pedos was quite hilarious - Brian Ribbon
Nobody called you king.
There's an operator layer running isp-cx-miami.net: the person provisioning servers across nine countries,naming them in a private inventory they thought no one would find, maintaining separate Mail-in-a-Box instances for Free Spirits, for the Visions of Alice cluster, for Alento's Frankfurt mail server. There's an infrastructure layer: aldns.org, fscodns.net, fstube.net, the Gitea instance at git.visionsofalice.com where the Alice-Coders dev team maintains private repositories. There's an organizational layer: Mu/MAP
Union, founded by Jim Burton, whose Newgon infrastructure spent two years hosting and funding a tactical disinformation operation on Twitter.
Brian is an articulate mouth piece who uses inflammatory statements for attention. Claiming to be a teacher for his very age of attraction. The network's technical infrastructure was built by someone with over 15 years of documented sysadmin activity, genuine expertise in DNS architecture, deliberate multi-jurisdiction operational security, and the resources to maintain 50+ servers across nine countries simultaneously. That person has been operating since at least 2009, years before brianribbon.com existed.
Brian Ribbon writes a blog on someone else's infrastructure. The investigation's interest in him is specific and narrow: he publicly boasts that he teaches sixth grade, he published an article titled "Let's get more MAPs in classrooms," and he gave an interview to a darknet CSAM site admin. That's the basis for his appearance in the investigation, not a theory about his technical role. Conflating "you wrote about my blog" with "you think I built all of this" is either a misreading or a deliberate deflection from the specific, narrow, and well-documented reasons he'd be included in an article on this ecosystem.
Now, that being said let me highlight 2 possible groups responsible for this cluster.
The Visions of Alice. alice-coders.net, which appeared on ns1.aldns.org in 2023, corresponds to git.visionsofalice.com - a private Gitea code repository hosting active software development for visionsofalice.com. The same cluster includes a self-hosted Vaultwarden password manager (bitwarden.visionsofalice.com). This is a development team maintaining shared codebases and credential infrastructure.
The alentogroup.org operator. The actual administrative identity behind the shared infrastructure has been documented through Mail-in-a-Box forum posts dating to 2018, a GitHub organization with ID 42585319, an IANA Private Enterprise Number (34974) registered under a pseudonym, and a stated operational security philosophy of deliberately choosing hosting outside the 14 Eyes intelligence-sharing alliance, a choice confirmed by the use of Romanian, Bulgarian, Lithuanian, and Vanuatu-incorporated providers across three generations of mail server infrastructure going back to 2016.
Before I go
Unsurprisingly, the man failed to persuade the bulletproof hosting provider to take down our legal content. The best he was able to muster was a French news article and debate on r/Epstein, the laughable lefty version of QAnon. I'm sure the complaints to our host would have been no surprise to them, nor to the NCMEC, as sites such as this receive constant reports both to providers and to law enforcement. Perhaps that says something about the legal status of our sites, and the immutable right to free speech to which a select few still subscribe. - Brian Ribbon
I'd like to post some quotes from a few of Brian Ribbon's posts on these forums and message boards to bolster my argument that his site only exists for the promotion of pro contact pedophilia.
Fragment, co-administrator of Mu and self-described co-founder alongside Brian Ribbon, is currently in prison for 2 years for the molestation of two 8th grade students (ages 13–14), both his students at school. Fragment is quoted saying ""I threw away what was a really great relationship over an orgasm. And not even mine." Brian's own response to this on MAP Union's forum wasn't concern, it was a scheduling note. His position isn't that these acts are wrong; it's that the punishment is disproportionate. His own MAP Manifesto says he doesn't believe "consensual" adult-minor sexual contact is "necessarily harmful." That's not someone with a platonic worldview.

This one is interesting. It follows the same mindset many men have on women, they're "asking for it" based on actions that are not at all sexual. Even calling him a "perv" while he's fawning over a child. The fact that an adult man attracted to adult women and an adult man attracted to male children both fall into the trap of "If I'm turned on then they're asking for it" is very interesting to me. Even watching a child play he considers "sexy", further proving that he has no intention of some imagined "platonic" relationship with these victims.
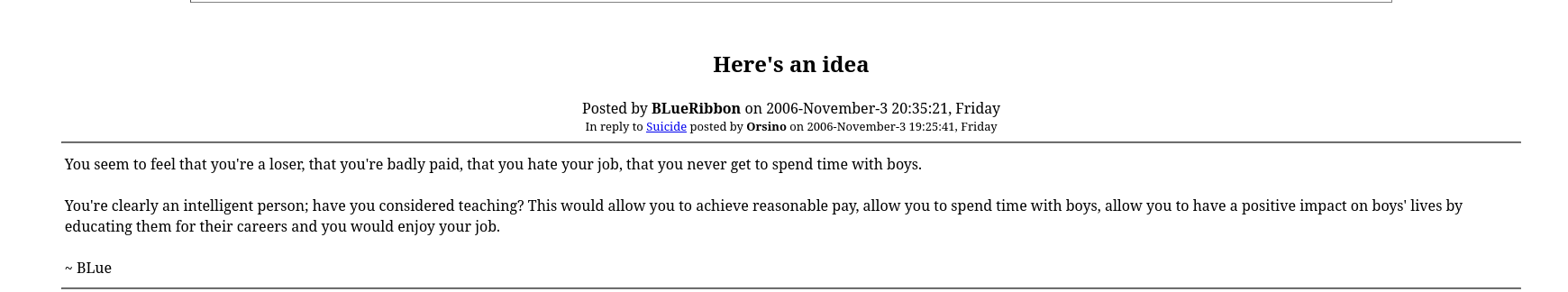
Even back in 2006 Brian was advocating for pedophiles to become teachers to have a stock of victims. Even stating he gets "depressed" without young friends which made it a necessity to move somewhere with more relaxed laws. But he is right that he didn't chose to have this attraction, it was created by external forces. But just like sexual sadists, being sexually frustrated isn't an excuse to abuse someone else, plain and simple. Brian argues that without sites like his, more offenders will move to the real world to commit their perversions. That argument is completely shadowed by the fact that he's apart of an infrastructure actively encouraging struggling pedophiles to not only surround themselves with children, but that their attraction is normal and should be encouraged.
To sum up, France moved in 24 hours. The US hasn't moved at all. Sharing
this helps, and to follow along with my work on Instagram @gpatricksec